Articles in Location Privacy

The 45-Second Trick For Identity Protection Tools
Older scams is among the most usual sorts of identification burglary $1.5 billion was swiped from over 2.4...
5 min read
30 Jan 2026
8 Simple Techniques For Identity Protection Tools
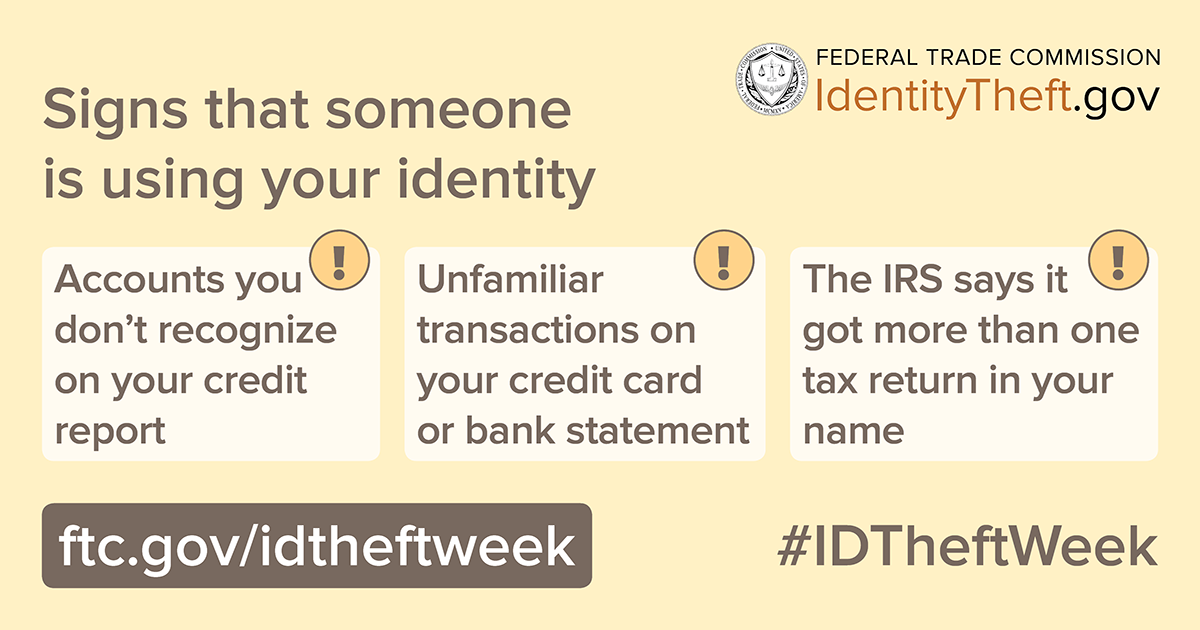
Once they have means to call you, someone could send you a counterfeit message regarding suspicious activity...
5 min read
29 Jan 2026
4 Easy Facts About Identity Protection Tools Described
The South Carolina Division of Consumer Matters' Identification Theft System ("the Device") aims to inform consumers...
7 min read
29 Jan 2026

The 10-Minute Rule for Identity Protection Tools
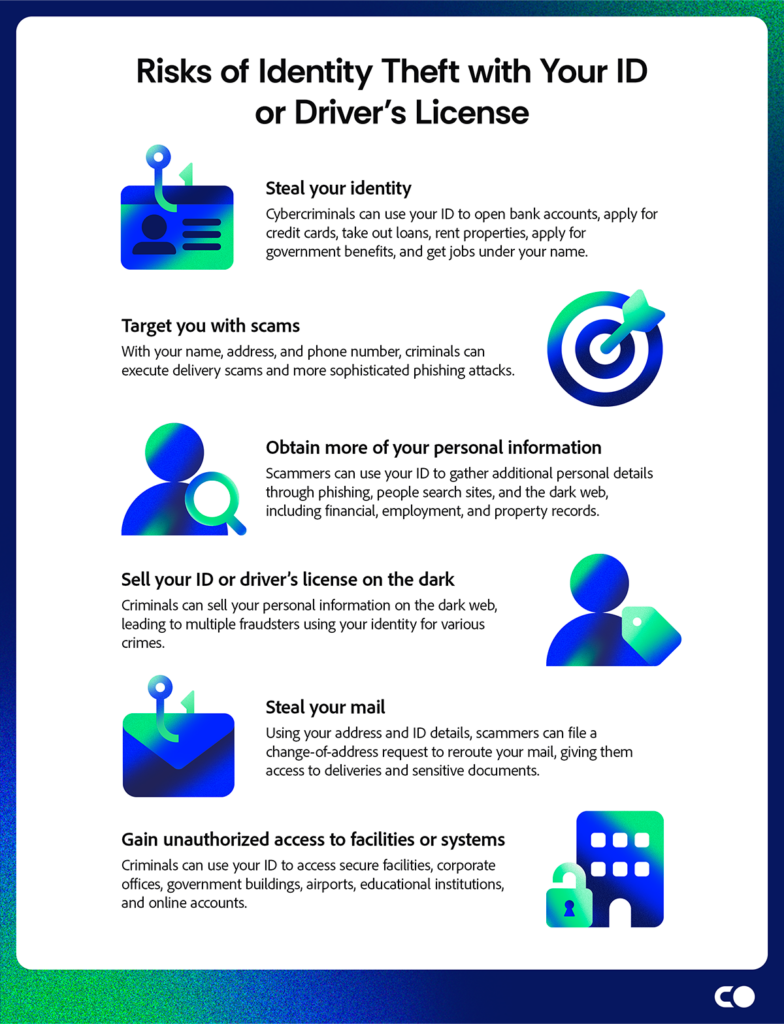
This circumstance is extremely unsafe since it will certainly be challenging to confirm that you didn't devote those criminal offenses because one more person...
5 min read
29 Jan 2026

The Main Principles Of Identity Protection Tools
We published all our info into the identity burglary security page and switched to the anti-virus device with one click to...
7 min read
28 Jan 2026

See This Report about Identity Protection Tools
Shed wage reimbursementNotary feesMailing costsPhone billsChild, spousal, and elderly careCredit tracking servicesLegal feesCosts of changing swiped papers (e.g., passport or...
5 min read
28 Jan 2026
The 9-Minute Rule for Identity Protection Tools
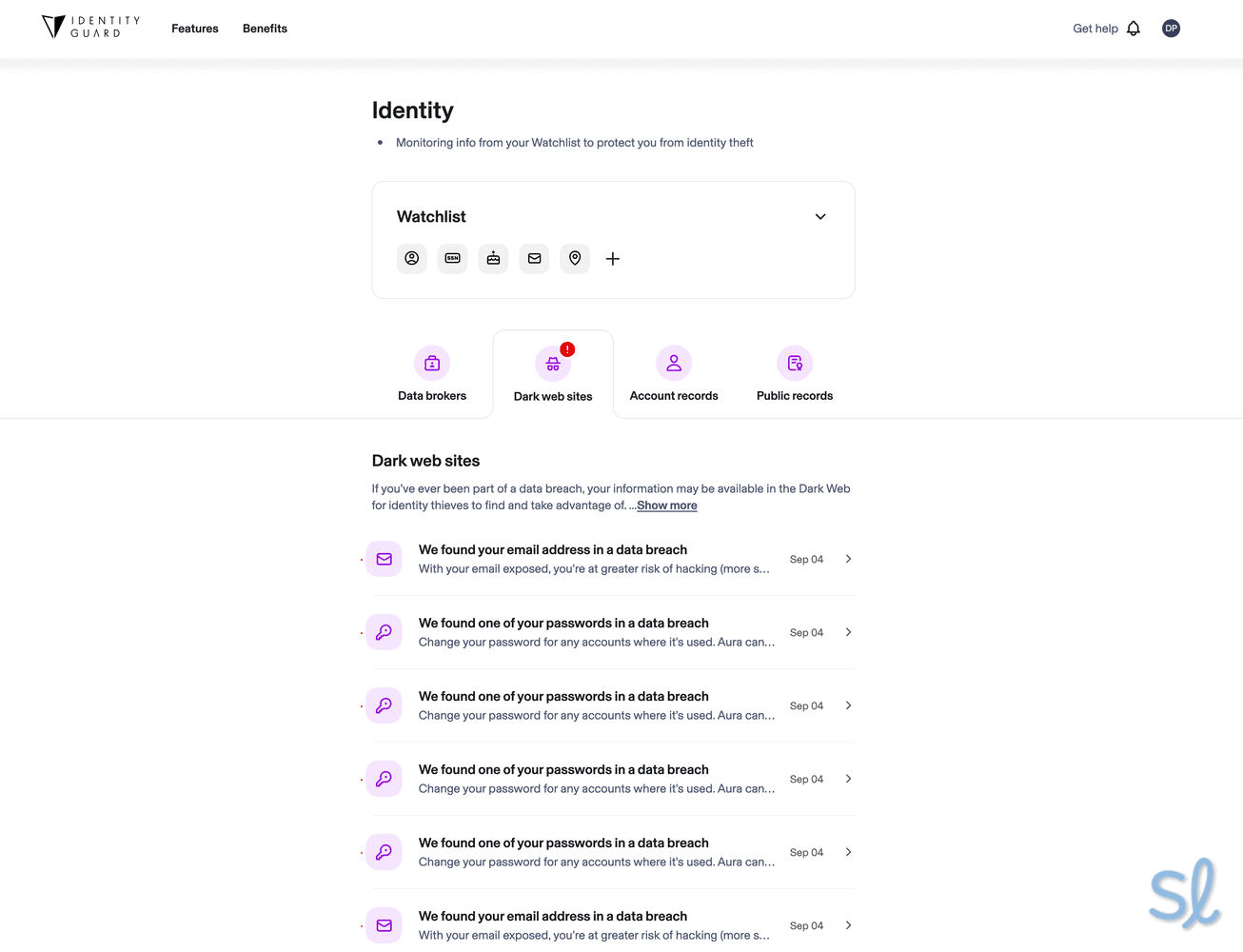
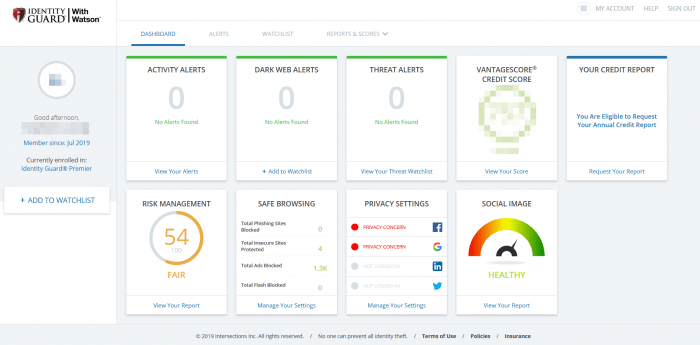
If budget's a priority, Aura and Identification Guard come in less expensive, yet if you do not mind buying costs security,...
5 min read
28 Jan 2026
Facts About Identity Protection Tools Revealed
Superior identification burglary defense and cybersecurity collection in one Up to $3 million insurance coverage Additional electronic protection attributes for children Artificial...
5 min read
27 Jan 2026
The smart Trick of Identity Protection Tools That Nobody is Talking About
Silver Gold Platinum Month-to-month $15.49 $21.49 $28.49 One year ordinary regular monthly cost $7.49 $10.49 $13.99 2 years...
5 min read
27 Jan 2026

Unknown Facts About Identity Protection Tools
Fast alerts All plans offer the same core attributes Consists of lots of cybersecurity functions Affordable strategies beginning at...
6 min read
26 Jan 2026